Authentication
To authenticate your webhooks, please follow these steps:
- Log in to the Liminal Platform.
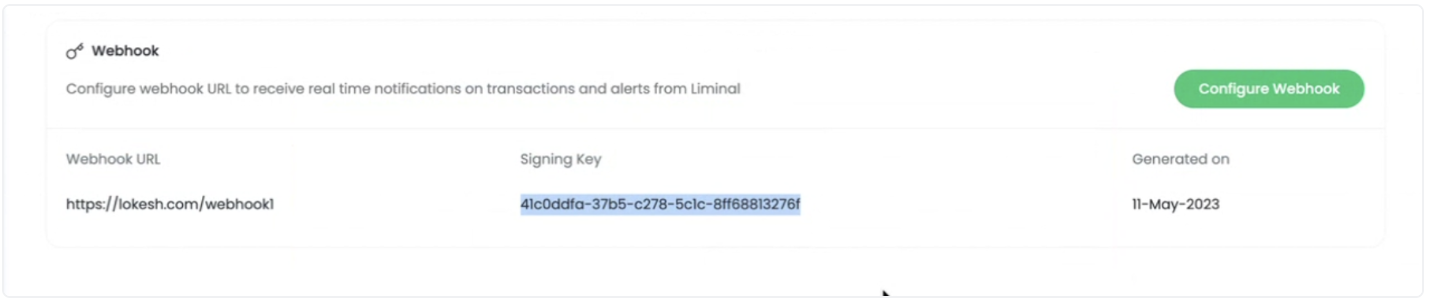
- Go to the 'dev' section located in the left navigation panel.
- Scroll down to the 'webhook URL' section.
- If the URL has already been registered, you'll find a signature there. This signature is used to authenticate your webhooks.
-
Client needs to implement the Generate Signature Method as given below. It ensures the authentication by passing 2 parameters, request body and signature. Client must implement the 'Generate Signature Method' as provided below. This method authenticates the process by taking two parameters - the request body and the signature.
The method is written in Node.js. However, if clients are able to translate this code into their preferred programming language, they can utilize a third-party framework or a different programming language to establish a webhook endpoint.
import * as crypto from "crypto"
const getSignature = (data: any, signingKey:string) => {
try {
let signature = crypto.createHmac('sha256', signingKey).update(JSON.stringify(data)).digest('hex');
return signature;
} catch (error) {
Logger.error(`Failed to get signature ${error}`);
}
}
router.post('YOUR-WEBHOOK-ENDPOINT', async (req: Request, res: Response) => {
// Read Header Value => Here you will recevie signature from Liminal Web App
let liminalSignatureHeaderValue:string=req.headers["x-liminal-signature"];
//Set Signature(Signing Key) value which you will get from Web UI(Setting=>WebHook Section)
let clientSignatureValue:string="YOUR-SIGNATURE-KEY";
// Read Request Body.
let transferStatusObj:any=req.body;
// Get Signature
let generatedSignature:string=getSignature(transferStatusObj,clientSignatureValue);
if(liminalSignatureHeaderValue===generatedSignature){
console.log(`Valid Signature`);
// Your Code [Data Insert]
}
else
{
console.log(`InValid Signature`);
}
}
The provided JavaScript code(line 1 to 10) defines a function getSignature that generates a cryptographic signature for a given data using a specific signing key. It uses the 'sha256' hashing algorithm to create a HMAC (Hash-based Message Authentication Code) and returns the digest as a hexadecimal string. If any error occurs during this process, it's caught and logged to the console. This signature can be used to ensure data integrity and authenticity.
The section of code spanning from line 12 to the end is dedicated to the creation of an endpoint responsible for handling webhook data. Specifically, at line 15, we focus on the retrieval of the Liminal signature from the request header, whereas line 16 underscores the requirement for the client to provide the signature generated through the web UI.
Upon proceeding to line 21, the code demonstrates the process of extracting webhook data from the request body. The subsequent line, line 24, signifies the critical step of validating the signature by utilizing both the request body and the client's signature key. It's important to note that further details about the GetSignature function can be found in the preceding paragraph.
Finally, lines 26 to 35 address the validation process. In the event that the Liminal signature matches the signature generated by the client, it is considered a valid signature. With a valid signature, the code allows for the implementation of custom logic within the associated 'if' block.
Note: Each client is assigned a unique signature.
